在 Kubernetes 集群的日常维护中,证书管理是一个不容忽视的关键环节。尤其是对于使用 kubeadm 工具部署的集群,其内置的证书机制有着明确的有效期限制。一旦证书过期,整个集群的通信与管控将陷入瘫痪。本文将深入解析 Kubernetes 的证书体系,手把手教你如何查看、续期证书,并探讨如何从源头设置“长期有效”的证书,避免未来可能出现的运维故障。
Kubernetes证书机制概览
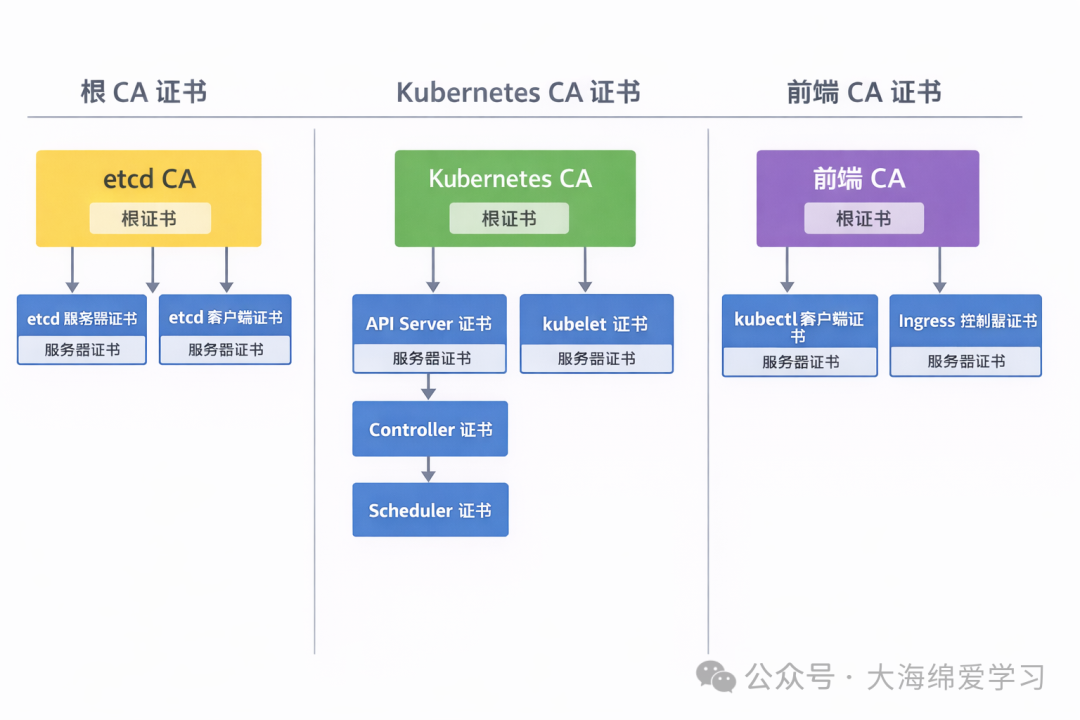
默认情况下,kubeadm 部署的集群证书通常存放在 /etc/kubernetes/pki/ 路径下。这些证书主要分为两大类:服务器证书和客户端证书,共同构成了集群内部安全通信的基石。
参考官方文档:https://kubernetes.io/zh-cn/docs/setup/best-practices/certificates/
服务器证书
-
API 服务器端点的证书
[root@k8s-master01 ~]# openssl x509 -in /etc/kubernetes/pki/apiserver.crt -text|head
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 3723707841031249294 (0x33ad448d68011d8e)
Signature Algorithm: sha256WithRSAEncryption
Issuer: CN = kubernetes
Validity
Not Before: Mar 17 12:11:04 2026 GMT
Not After : Mar 17 12:16:04 2027 GMT
Subject: CN = kube-apiserver
-
etcd 服务器的服务器证书
[root@k8s-master01 ~]# openssl x509 -in /etc/kubernetes/pki/etcd/ca.crt -text|head
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 3081390123443469926 (0x2ac34bfdca3ebe66)
Signature Algorithm: sha256WithRSAEncryption
Issuer: CN = etcd-ca
Validity
Not Before: Sep 27 07:35:28 2025 GMT
Not After : Sep 25 07:40:28 2035 GMT
Subject: CN = etcd-ca
-
每个 kubelet 的服务器证书(每个节点运行一个 kubelet)
[root@k8s-master01 ~]# openssl x509 -in /var/lib/kubelet/pki/kubelet.crt -text |head
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 112909339695175473 (0x19122723c5ad731)
Signature Algorithm: sha256WithRSAEncryption
Issuer: CN = k8s-master01.dinginx.org-ca@1758958833
Validity
Not Before: Sep 27 06:40:33 2025 GMT
Not After : Sep 27 06:40:33 2026 GMT
Subject: CN = k8s-master01.dinginx.org@1758958833
-
可选的前端代理的服务器证书
[root@k8s-master01 ~]# openssl x509 -in /etc/kubernetes/pki/front-proxy-ca.crt -text|head
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 6133933849525219158 (0x55201c5650b1ef56)
Signature Algorithm: sha256WithRSAEncryption
Issuer: CN = front-proxy-ca
Validity
Not Before: Sep 27 07:35:28 2025 GMT
Not After : Sep 25 07:40:28 2035 GMT
Subject: CN = front-proxy-ca
客户端证书
- 针对每个 kubelet 的客户端证书,用于 API 服务器作为 Kubernetes API 的客户端进行身份验证
- 每个 API 服务器的客户端证书,用于向 etcd 进行身份验证
- 控制器管理器与 API 服务器进行安全通信的客户端证书
- 调度程序与 API 服务器进行安全通信的客户端证书
- 客户端证书(每个节点一个),用于 kube-proxy 向 API 服务器进行身份验证
- 集群管理员向 API 服务器进行身份验证的可选客户端证书
- 前端代理的可选客户端证书
举例说明
如果你是kubeadm部署的集群,证书会自动生成。以下是根CA的路径和信息示例:
# 存放路径
[root@k8s-master01 ~]# cat /etc/kubernetes/pki/
apiserver-etcd-client.crt apiserver-kubelet-client.key ca.crt front-proxy-ca.crt front-proxy-client.key
apiserver-etcd-client.key apiserver.crt ca.key front-proxy-ca.key sa.key
apiserver-kubelet-client.crt apiserver.key etcd/ front-proxy-client.crt sa.pub
[root@k8s-master01 ~]# ls /etc/kubernetes/pki/ca.crt
# 查看详细信息,默认有效期十年
[root@k8s-master01 ~]# openssl x509 -in /etc/kubernetes/pki/ca.crt -text
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 7010362768650409617 (0x6149cfcbac081691)
Signature Algorithm: sha256WithRSAEncryption
Issuer: CN = kubernetes
Validity
Not Before: Sep 27 07:35:28 2025 GMT
Not After : Sep 25 07:40:28 2035 GMT
Subject: CN = kubernetes
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (2048 bit)
Modulus:
00:e2:62:6d:e6:9b:a4:9a:dd:fa:c2:1e:87:ab:6c:
ad:da:2c:b2:ad:c4:ea:8b:f4:6c:0c:47:13:ce:7e:
14:a7:3c:12:d5:b6:ef:38:61:60:66:28:b2:8e:a8:
95:15:cb:77:a9:83:48:fb:cc:64:67:87:3a:41:a4:
3d:cb:3a:e2:7b:f2:98:7f:3b:f1:b8:3a:20:24:56:
3c:9f:9f:21:26:04:b5:b0:48:f2:2a:2d:2c:41:b6:
41:c9:4d:0c:90:c3:4a:8b:40:82:26:03:50:de:55:
35:fe:a2:f2:0c:27:df:e9:5e:dd:37:aa:33:1c:4c:
87:d1:89:1e:b3:86:3e:97:7c:20:de:ef:5e:fb:78:
93:79:37:80:ea:bf:c7:f6:ad:da:19:bc:c2:58:3c:
ea:44:bf:97:c1:15:85:8b:e0:2c:56:0c:55:92:f4:
40:97:67:02:04:7a:02:76:29:d0:3b:70:30:cb:68:
99:57:1b:05:d6:b1:2a:de:0a:1e:b6:51:f2:90:f1:
0a:e5:0e:f1:0d:a0:61:5c:52:7f:04:dc:4d:c4:78:
42:1e:74:7a:b1:1e:92:58:5a:80:11:2c:90:d2:61:
c5:cd:83:df:88:a8:4d:27:f1:86:39:9c:7f:4c:f6:
5c:98:fa:14:0b:70:00:0e:31:99:3c:bf:2e:59:5c:
12:6b
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Key Usage: critical
Digital Signature, Key Encipherment, Certificate Sign
X509v3 Basic Constraints: critical
CA:TRUE
X509v3 Subject Key Identifier:
01:AD:FF:24:AA:29:29:D8:66:DE:95:6D:31:6B:0D:CD:34:FC:49:D1
X509v3 Subject Alternative Name:
DNS:kubernetes
Signature Algorithm: sha256WithRSAEncryption
Signature Value:
7d:1b:15:45:c5:2e:08:e2:50:e4:19:de:ff:af:e2:53:21:d3:
4b:12:79:f9:1a:0d:88:a9:e9:fc:bf:56:74:29:26:06:46:0b:
4b:3a:74:ce:9e:8f:2f:2c:d3:5e:eb:11:84:e0:ab:c5:70:be:
82:1d:56:7a:ec:ae:16:1f:71:d6:47:a5:30:c9:49:59:a4:c5:
ab:37:bc:04:7b:31:43:b9:b2:65:ee:d9:b4:f7:d4:59:c0:c1:
be:81:fb:c3:9f:c2:de:58:27:b0:37:fb:fa:5e:44:b0:bb:2e:
ee:76:c2:70:b5:30:f6:5e:09:46:22:b6:8a:0c:a1:98:23:0e:
6f:bb:91:23:18:0c:fb:56:a4:9f:af:bd:12:96:ad:82:d9:19:
e2:62:71:db:9e:4b:89:93:43:c3:a1:6c:e6:c0:24:c3:3a:73:
4f:aa:e3:5d:57:13:98:07:e4:2b:aa:05:5c:01:22:3c:6d:4f:
1a:54:ad:ec:99:2d:cd:9e:04:bf:b4:41:ed:fe:51:a6:64:14:
11:f8:9e:62:34:22:72:fa:07:20:74:5e:12:b9:31:6f:31:a7:
12:a2:19:5a:a5:94:ce:4c:ec:80:53:37:8d:eb:85:38:9b:be:
d1:96:6b:c1:5c:b9:b1:65:2e:54:39:d5:0f:cb:94:e7:2b:4a:
6a:c2:10:6d
-----BEGIN CERTIFICATE-----
MIIDBTCCAe2gAwIBAgIIYUnPy6wIFpEwDQYJKoZIhvcNAQELBQAwFTETMBEGA1UE
AxMKa3ViZXJuZXRlczAeFw0yNTA5MjcwNzM1MjhaFw0zNTA5MjUwNzQwMjhaMBUx
EzARBgNVBAMTCmt1YmVybmV0ZXMwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAwggEK
AoIBAQDiYm3mm6Sa3frCHoerbK3aLLKtxOqL9GwMRxPOfhSnPBLVtu84YWBmKLKO
qJUVy3epg0j7zGRnhzpBpD3LOuJ78ph/O/G4OiAkVjyfnyEmBLWwSPIqLSxBtkHJ
TQyQw0qLQIImA1DeVTX+ovIMJ9/pXt03qjMcTIfRiR6zhj6XfCDe7177eJN5N4Dq
v8f2rdoZvMJYPOpEv5fBFYWL4CxWDFWS9ECXZwIEegJ2KdA7cDDLaJlXGwXWsSre
Ch62UfKQ8QrlDvENoGFcUn8E3E3EeEIedHqxHpJYWoARLJDSYcXNg9+IqE0n8YY5
nH9M9lyY+hQLcAAOMZk8vy5ZXBJrAgMBAAGjWTBXMA4GA1UdDwEB/wQEAwICpDAP
BgNVHRMBAf8EBTADAQH/MB0GA1UdDgQWBBQBrf8kqikp2GbelW0xaw3NNPxJ0TAV
BgNVHREEDjAMggprdWJlcm5ldGVzMA0GCSqGSIb3DQEBCwUAA4IBAQB9GxVFxS4I
4lDkGd7/r+JTIdNLEnn5Gg2Iqen8v1Z0KSYGRgtLOnTOno8vLNNe6xGE4KvFcL6C
HVZ67K4WH3HWR6UwyUlZpMWrN7wEezFDubJl7tm099RZwMG+gfvDn8LeWCewN/v6
XkSwuy7udsJwtTD2XglGIraKDKGYIw5vu5EjGAz7VqSfr70Slq2C2RniYnHbnkuJ
k0PDoWzmwCTDOnNPquNdVxOYB+QrqcVcASI8bU8aVK3smS3NngS/tEHt/lGmZBQR
+J5iNCJy+gcgdF4SuTFvMacSohlapZTOTOyAUzeN64U4m77RlmvBXLmxZS5UOdUP
y5TnK0pqwhBt
-----END CERTIFICATE-----
Kubernetes证书续期实战
基于kubeadm安装的k8s集群,默认的根CA有效期为10年,而各个核心组件使用的证书有效期仅为1年。因此,定期检查并续期证书是保障集群稳定运行的必要操作。
查看证书有效期
第一步永远是确认证书状态。使用 kubeadm certs check-expiration 命令可以清晰列出所有证书的过期时间。
# 查看证书有效期
[root@k8s-master01 ~]# kubeadm certs check-expiration
[check-expiration] Reading configuration from the "kubeadm-config" ConfigMap in namespace "kube-system"...
[check-expiration] Use 'kubeadm init phase upload-config kubeadm --config your-config-file' to re-upload it.
CERTIFICATE EXPIRES RESIDUAL TIME CERTIFICATE AUTHORITY EXTERNALLY MANAGED
admin.conf Mar 17, 2027 12:16 UTC 363d ca no
apiserver Mar 17, 2027 12:16 UTC 363d ca no
apiserver-etcd-client Mar 17, 2027 12:16 UTC 363d etcd-ca no
apiserver-kubelet-client Mar 17, 2027 12:16 UTC 363d ca no
controller-manager.conf Mar 17, 2027 12:16 UTC 363d ca no
etcd-healthcheck-client Mar 17, 2027 12:16 UTC 363d etcd-ca no
etcd-peer Mar 17, 2027 12:16 UTC 363d etcd-ca no
etcd-server Mar 17, 2027 12:16 UTC 363d etcd-ca no
front-proxy-client Mar 17, 2027 12:16 UTC 363d front-proxy-ca no
scheduler.conf Mar 17, 2027 12:16 UTC 363d ca no
super-admin.conf Mar 17, 2027 12:16 UTC 363d ca no
CERTIFICATE AUTHORITY EXPIRES RESIDUAL TIME EXTERNALLY MANAGED
ca Sep 25, 2035 07:40 UTC 9y no
etcd-ca Sep 25, 2035 07:40 UTC 9y no
front-proxy-ca Sep 25, 2035 07:40 UTC 9y no
## 这里因集群是25年创建的,故根ca至2035年到期;
集群证书即将过期时的续约操作
当发现证书剩余时间不足时(例如少于90天),应及时进行续期。kubeadm certs renew 命令是专门用于此任务的工具。
# 采用kubeadm certs renew自定续期一年
[root@k8s-master01 ~]# kubeadm certs renew -h
Renew certificates for a Kubernetes cluster
Usage:
kubeadm certs renew [flags]
kubeadm certs renew [command]
Available Commands:
admin.conf Renew the certificate embedded in the kubeconfig file for the admin to use and for kubeadm itself
all Renew all available certificates
apiserver Renew the certificate for serving the Kubernetes API
apiserver-etcd-client Renew the certificate the apiserver uses to access etcd
apiserver-kubelet-client Renew the certificate for the API server to connect to kubelet
controller-manager.conf Renew the certificate embedded in the kubeconfig file for the controller manager to use
etcd-healthcheck-client Renew the certificate for liveness probes to healthcheck etcd
etcd-peer Renew the certificate for etcd nodes to communicate with each other
etcd-server Renew the certificate for serving etcd
front-proxy-client Renew the certificate for the front proxy client
scheduler.conf Renew the certificate embedded in the kubeconfig file for the scheduler manager to use
super-admin.conf Renew the certificate embedded in the kubeconfig file for the super-admin
Flags:
-h, --help help for renew
Global Flags:
--rootfs string The path to the 'real' host root filesystem. This will cause kubeadm to chroot into the provided path.
-v, --v Level number for the log level verbosity
--vmodule moduleSpec comma-separated list of pattern=N settings for file-filtered logging
Use "kubeadm certs renew [command] --help" for more information about a command.
error:
error: subcommand is required
To see the stack trace of this error execute with --v=5 or higher
## 这里可以指定要更新的证书,我们这里直接选择all
更新证书并生效
续期操作完成后,必须重启相关组件才能让新证书生效。
# 执行更新指令,签发所有文件的证书
## 如果是多节点高可用集群需在所有的控制平面执行
[root@k8s-master01 ~]# kubeadm certs renew all
[renew] Reading configuration from the “kubeadm-config” ConfigMap in namespace “kube-system”...
[renew] Use 'kubeadm init phase upload-config kubeadm --config your-config-file’ to re-upload it.
certificate embedded in the kubeconfig file for the admin to use and for kubeadm itself renewed
certificate for serving the Kubernetes API renewed
certificate the apiserver uses to access etcd renewed
certificate for the API server to connect to kubelet renewed
certificate embedded in the kubeconfig file for the controller manager to use renewed
certificate for liveness probes to healthcheck etcd renewed
certificate for etcd nodes to communicate with each other renewed
certificate for serving etcd renewed
certificate for the front proxy client renewed
certificate embedded in the kubeconfig file for the scheduler manager to use renewed
certificate embedded in the kubeconfig file for the super-admin renewed
Done renewing certificates. You must restart the kube-apiserver, kube-controller-manager, kube-scheduler and etcd, so that they can use the new certificates.
## 这里显示证书自动更新完成,需要重启kube-apiserver, kube-controller-manager, kube-scheduler, etcd的pod资源才会生效。
## 上述操作不会续签kubelet证书,一般也无需手动续签,在到期前30-120内会自动出发续签的机制自动续签;
## 如果kubelet需要手动更新,
[root@k8s-master01 ~]# kubeadm init --kubernetes-version=v1.35.0 phase kubeconfig all
# 检查证书有效期
[root@k8s-master01 ~]# kubeadm certs check-expiration
[check-expiration] Reading configuration from the “kubeadm-config” ConfigMap in namespace “kube-system”...
[check-expiration] Use 'kubeadm init phase upload-config kubeadm --config your-config-file’ to re-upload it.
CERTIFICATE EXPIRES RESIDUAL TIME CERTIFICATE AUTHORITY EXTERNALLY MANAGED
admin.conf Mar 19, 2027 11:58 UTC 364d ca no
apiserver Mar 19, 2027 11:58 UTC 364d ca no
apiserver-etcd-client Mar 19, 2027 11:58 UTC 364d etcd-ca no
apiserver-kubelet-client Mar 19, 2027 11:58 UTC 364d ca no
controller-manager.conf Mar 19, 2027 11:58 UTC 364d ca no
etcd-healthcheck-client Mar 19, 2027 11:58 UTC 364d etcd-ca no
etcd-peer Mar 19, 2027 11:58 UTC 364d etcd-ca no
etcd-server Mar 19, 2027 11:58 UTC 364d etcd-ca no
front-proxy-client Mar 19, 2027 11:58 UTC 364d front-proxy-ca no
scheduler.conf Mar 19, 2027 11:58 UTC 364d ca no
super-admin.conf Mar 19, 2027 11:58 UTC 364d ca no
CERTIFICATE AUTHORITY EXPIRES RESIDUAL TIME EXTERNALLY MANAGED
ca Sep 25, 2035 07:40 UTC 9y no
etcd-ca Sep 25, 2035 07:40 UTC 9y no
front-proxy-ca Sep 25, 2035 07:40 UTC 9y no
# 重启资源,实质就是删除资源等待自动创建即可;生产环境建议选择空闲时段进行更新,
[root@k8s-master01 ~]# kubectl delete pods -n kube-system -l ‘component in (kube-apiserver,kube-controller-manager,kube-scheduler,etcd)’ --grace-period=0
pod “etcd-k8s-master01.dinginx.org” deleted from kube-system namespace
pod “kube-apiserver-k8s-master01.dinginx.org” deleted from kube-system namespace
pod “kube-controller-manager-k8s-master01.dinginx.org” deleted from kube-system namespace
pod “kube-scheduler-k8s-master01.dinginx.org” deleted from kube-system namespace
# 查看组件状态
[root@k8s-master01 ~]# kubectl get pods -n kube-system -l ‘component in (kube-apiserver,kube-controller-manager,kube-scheduler,etcd)’
NAME READY STATUS RESTARTS AGE
etcd-k8s-master01.dinginx.org 1/1 Running 12 (6d13h ago) 53s
kube-apiserver-k8s-master01.dinginx.org 1/1 Running 6 (6d13h ago) 53s
kube-controller-manager-k8s-master01.dinginx.org 1/1 Running 1 (2d18h ago) 53s
kube-scheduler-k8s-master01.dinginx.org 1/1 Running 69 (4d11h ago) 53s
# 更新授权.kube/config文件
[root@k8s-master01 ~]# ll /etc/kubernetes/admin.conf
-rw------- 1 root root 5647 Mar 22 11:28 /etc/kubernetes/admin.conf
[root@k8s-master01 ~]# ls .kube/config -hl
-rw------- 1 root root 5.6K Mar 17 23:43 .kube/config
## 更新证书
[root@k8s-master01 ~]# cp /etc/kubernetes/admin.conf .kube/config
## 验证
[root@k8s-master01 ~]# ls .kube/config -hl
-rw------- 1 root root 5.6K Mar 22 11:29 .kube/config
集群证书已过期时的紧急续约
如果因为疏忽导致证书已经过期,集群将无法访问。这时需要一套略有不同的恢复流程。
模拟故障
首先,我们通过修改系统时间来模拟证书过期的场景。
# 步骤和续约类似,但是证书kubeadm certs renew之后只会更新证书,kubelet客户端证书不会更新
# 修改系统时间模拟故障
[root@k8s-master01 ~]# date -s '2027-4-29 12:59:20'
Thu Apr 29 12:59:20 CST 2027
[root@k8s-master01 ~]# date
Thu Apr 29 12:59:22 CST 2027
## 验证无法访问资源
[root@k8s-master01 ~]# kubectl get pods
E0429 12:59:45.948061 802272 memcache.go:265] "Unhandled Error" err="couldn’t get current server API group list: Get \"https://kubeapi.dinginx.org:6443/api?timeout=32s\": tls: failed to verify certificate: x509: certificate has expired or is not yet valid: current time 2027-04-29T12:59:45+08:00 is after 2027-03-22T03:28:38Z"
E0429 12:59:45.951098 802272 memcache.go:265] "Unhandled Error" err="couldn’t get current server API group list: Get \"https://kubeapi.dinginx.org:6443/api?timeout=32s\": tls: failed to verify certificate: x509: certificate has expired or is not yet valid: current time 2027-04-29T12:59:45+08:00 is after 2027-03-22T03:28:38Z"
E0429 12:59:45.954372 802272 memcache.go:265] "Unhandled Error" err="couldn’t get current server API group list: Get \"https://kubeapi.dinginx.org:6443/api?timeout=32s\": tls: failed to verify certificate: x509: certificate has expired or is not yet valid: current time 2027-04-29T12:59:45+08:00 is after 2027-03-22T03:28:38Z"
E0429 12:59:45.958004 802272 memcache.go:265] "Unhandled Error" err="couldn’t get current server API group list: Get \"https://kubeapi.dinginx.org:6443/api?timeout=32s\": tls: failed to verify certificate: x509: certificate has expired or is not yet valid: current time 2027-04-29T12:59:45+08:00 is after 2027-03-22T03:28:38Z"
E0429 12:59:45.960758 802272 memcache.go:265] "Unhandled Error" err="couldn’t get current server API group list: Get \"https://kubeapi.dinginx.org:6443/api?timeout=32s\": tls: failed to verify certificate: x509: certificate has expired or is not yet valid: current time 2027-04-29T12:59:45+08:00 is after 2027-03-22T03:28:38Z"
Unable to connect to the server: tls: failed to verify certificate: x509: certificate has expired or is not yet valid: current time 2027-04-29T12:59:45+08:00 is after 2027-03-22T03:28:38
查看证书信息
此时,kubeadm certs check-expiration 命令会显示证书已失效。
[check-expiration] Error reading configuration from the Cluster. Falling back to default configuration
CERTIFICATE EXPIRES RESIDUAL TIME CERTIFICATE AUTHORITY EXTERNALLY MANAGED
admin.conf Mar 22, 2027 03:28 UTC <invalid> ca no
apiserver Mar 22, 2027 03:28 UTC <invalid> ca no
apiserver-etcd-client Mar 22, 2027 03:28 UTC <invalid> etcd-ca no
apiserver-kubelet-client Mar 22, 2027 03:28 UTC <invalid> ca no
controller-manager.conf Mar 22, 2027 03:28 UTC <invalid> ca no
etcd-healthcheck-client Mar 22, 2027 03:28 UTC <invalid> etcd-ca no
etcd-peer Mar 22, 2027 03:28 UTC <invalid> etcd-ca no
etcd-server Mar 22, 2027 03:28 UTC <invalid> etcd-ca no
front-proxy-client Mar 22, 2027 03:28 UTC <invalid> front-proxy-ca no
scheduler.conf Mar 22, 2027 03:28 UTC <invalid> ca no
super-admin.conf Mar 22, 2027 03:28 UTC <invalid> ca no
CERTIFICATE AUTHORITY EXPIRES RESIDUAL TIME EXTERNALLY MANAGED
ca Sep 25, 2035 07:40 UTC 8y no
etcd-ca Sep 25, 2035 07:40 UTC 8y no
front-proxy-ca Sep 25, 2035 07:40 UTC 8y no
续签证书
证书虽过期,但只要根CA未过期,我们仍然可以使用 kubeadm certs renew 命令强制续签。
# 更新所有证书
[root@k8s-master01 ~]# kubeadm certs renew all
[renew] Reading configuration from the "kubeadm-config" ConfigMap in namespace "kube-system"...
[renew] Use 'kubeadm init phase upload-config kubeadm --config your-config-file' to re-upload it.
[renew] Error reading configuration from the Cluster. Falling back to default configuration
certificate embedded in the kubeconfig file for the admin to use and for kubeadm itself renewed
certificate for serving the Kubernetes API renewed
certificate the apiserver uses to access etcd renewed
certificate for the API server to connect to kubelet renewed
certificate embedded in the kubeconfig file for the controller manager to use renewed
certificate for liveness probes to healthcheck etcd renewed
certificate for etcd nodes to communicate with each other renewed
certificate for serving etcd renewed
certificate for the front proxy client renewed
certificate embedded in the kubeconfig file for the scheduler manager to use renewed
certificate embedded in the kubeconfig file for the super-admin renewed
Done renewing certificates. You must restart the kube-apiserver, kube-controller-manager, kube-scheduler and etcd, so that they can use the new certificates.
# 验证证书已更新
[root@k8s-master01 ~]# kubeadm certs check-expiration
[check-expiration] Reading configuration from the "kubeadm-config" ConfigMap in namespace "kube-system"...
[check-expiration] Use 'kubeadm init phase upload-config kubeadm --config your-config-file' to re-upload it.
CERTIFICATE EXPIRES RESIDUAL TIME CERTIFICATE AUTHORITY EXTERNALLY MANAGED
admin.conf Apr 28, 2028 05:04 UTC 364d ca no
apiserver Apr 28, 2028 05:04 UTC 364d ca no
apiserver-etcd-client Apr 28, 2028 05:04 UTC 364d etcd-ca no
apiserver-kubelet-client Apr 28, 2028 05:04 UTC 364d ca no
controller-manager.conf Apr 28, 2028 05:04 UTC 364d ca no
etcd-healthcheck-client Apr 28, 2028 05:04 UTC 364d etcd-ca no
etcd-peer Apr 28, 2028 05:04 UTC 364d etcd-ca no
etcd-server Apr 28, 2028 05:04 UTC 364d etcd-ca no
front-proxy-client Apr 28, 2028 05:04 UTC 364d front-proxy-ca no
scheduler.conf Apr 28, 2028 05:04 UTC 364d ca no
super-admin.conf Apr 28, 2028 05:04 UTC 364d ca no
CERTIFICATE AUTHORITY EXPIRES RESIDUAL TIME EXTERNALLY MANAGED
ca Sep 25, 2035 07:40 UTC 8y no
etcd-ca Sep 25, 2035 07:40 UTC 8y no
front-proxy-ca Sep 25, 2035 07:40 UTC 8y no
#此操作不会更新 kubelet 证书,会导致集群状态 NotReady ,节点 kubelet.services 状态异常,需手动更新
[root@k8s-master01 ~]# kubectl get nodes
NAME STATUS ROLES AGE VERSION
k8s-master01.dinginx.org Ready control-plane 578d v1.35.0
k8s-node01.dinginx.org NotReady <none> 578d v1.35.0
k8s-node02.dinginx.org NotReady <none> 578d v1.35.0
k8s-node03.dinginx.org NotReady <none> 415d v1.35.0
手动更新kubelet证书(关键步骤)
如输出所示,kubeadm certs renew 不会自动更新各个节点上的kubelet客户端证书,这会导致工作节点状态变为 NotReady。这是一项典型的运维故障处理任务,需要手动介入。
# 查看kubelet证书
[root@k8s-master01 ~]# ls /etc/kubernetes/kubelet.conf -hl
-rw------- 1 root root 2.0K Sep 27 2025 /etc/kubernetes/kubelet.conf
[root@k8s-master01 ~]# cat /etc/kubernetes/kubelet.conf
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURCVENDQWUyZ0F3SUJBZ0lJWVVuUHk2d0lGcEV3RFFZSktvWklodmNOQVFFTEJRQXdGVEVUTUJFR0ExVUUKQXhNS2EzVmlaWEp1WlhSbGN6QWVGdzB5TlRBNU1qY3dOek0xTWpoYUZ3MHpOVEE1TWpVd056UXdNamhhTUJVeApFekFSQmdOVkJBTVRDbXQxWW1WeWJtVjBaWE13Z2dFaU1BMEdDU3FHU0liM0RRRUJBUVVBQTRJQkR3QXdnZ0VLCkFvSUJBUURpWW0zbW02U2EzZnJDSG9lcmJLM2FMTEt0eE9xTDlHd01SeFBPZmhTblBCTFZ0dTg0WVdCbUtMS08KcUpVVnkzZXBnMGo3ekdSbmh6cEJwRDNMT3VKNzhwaC9PL0c0T2lBa1ZqeWZueUVtQkxXd1NQSXFMU3hCdGtISgpUUXlRdzBxTFFJSW1BMURlVlRYK292SU1KOS9wWHQwM3FqTWNUSWZSaVI2emhqNlhmQ0RlNzE3N2VKTjVONERxCnY4ZjJyZG9adk1KWVBPcEV2NWZCRllXTDRDeFdERldTOUVDWFp3SUVlZ0oyS2RBN2NERExhSmxYR3dYV3NTcmUKQ2g2MlVmS1E4UXJsRHZFTm9HRmNVbjhFM0UzRWVFSWVkSHF4SHBKWVdvQVJMSkRTWWNYTmc5K0lxRTBuOFlZNQpuSDlNOWx5WStoUUxjQUFPTVprOHZ5NVpYQkpyQWdNQkFBR2pXVEJYTUE0R0ExVWREd0VCL3dRRUF3SUNwREFQCkJnTlZIUk1CQWY4RUJUQURBUUgvTUIwR0ExVWREZ1FXQkJRQnJmOGtxaWtwMkdiZWxXMHhhdzNOTlB4SjBUQVYKQmdOVkhSRUVEakFNZ2dwcmRXSmxjbTVsZEdWek1BMEdDU3FHU0liM0RRRUJDd1VBQTRJQkFRQjlHeFZGeFM0SQo0bERrR2Q3L3IrSlRJZE5MRW5uNUdnMklxZW44djFaMEtTWUdSZ3RMT25UT25vOHZMTk5lNhhHRTRLdkZjTDZDCkhWWjY3SzRXSDNIV1I2VXd5VWxacE1Xck43d0VlekZEdWJKbDd0bTA5OVJad01HK2dmdkRuOExlV0Nld04vdjYKWGtTd3V5N3Vkc0p3dFREMlhnbEdJcmFLREtHWUl3NXZ1NUVqR0F6N1ZxU2ZyNzBTbHEyQzJSbmlZbkhibmt1SgprMFBEb1d6bXdDVERPbk5QcXVOZFZ4T1lCK1FycWdWY0FTSThiVThhVkszc21TM05uZ1MvdEVIdC9sR21aQlFSCitKNWlOQ0p5K2djZ2RGNFN1VEZ2TWFjU29obGFwWlRPVE95QVV6ZU42NFU0bTc3UmxtdkJYTG14WlM1VU9kVVAKeTVUbkswcHF3aEJ0Ci0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K
server: https://11.0.1.10:6443
name: kubernetes
contexts:
- context:
cluster: kubernetes
user: system:node:k8s-master01.dinginx.org
name: system:node:k8s-master01.dinginx.org@kubernetes
current-context: system:node:k8s-master01.dinginx.org@kubernetes
kind: Config
users:
- name: system:node:k8s-master01.dinginx.org
user:
client-certificate: /var/lib/kubelet/pki/kubelet-client-current.pem
client-key: /var/lib/kubelet/pki/kubelet-client-current.pem
# 查看证书认证信息,是有kubernetes CA颁发的证书
[root@k8s-master01 ~]# echo LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURCVENDQWUyZ0F3SUJBZ0lJWVVuUHk2d0lGcEV3RFFZSktvWklodmNOQVFFTEJRQXdGVEVUTUJFR0ExVUUKQXhNS2EzVmlaWEp1WlhSbGN6QWVGdzB5TlRBNU1qY3dOek0xTWpoYUZ3MHpOVEE1TWpVd056UXdNamhhTUJVeApFekFSQmdOVkJBTVRDbXQxWW1WeWJtVjBaWE13Z2dFaU1BMEdDU3FHU0liM0RRRUJBUVVBQTRJQkR3QXdnZ0VLCkFvSUJBUURpWW0zbW02U2EzZnJDSG9lcmJLM2FMTEt0eE9xTDlHd01SeFBPZmhTblBCTFZ0dTg0WVdCbUtMS08KcUpVVnkzZXBnMGo3ekdSbmh6cEJwRDNMT3VKNzhwaC9PL0c4T2lBa1ZqeWZueUVtQkxXd1NQSXFMU3hCdGtISgpUUXlRdzBxTFFJSW1BMURlVlRYK292SU1KOS9wWHQwM3FqTWNUSWZSaVI2emhqNlhmQ0RlNzE3N2VKTjVONERxCnY4ZjJyZG9adk1KWVBPcEV2NWZCRllXTDRDeFdERldTOUVDWFp3SUVlZ0oyS2RBN2NERExhSmxYR3dYV3NTcmUKQ2g2MlVmS1E4UXJsRHZFTm9HRmNVbjhFM0UzRWVFSWVkSHF4SHBKWVdvQVJMSkRTWWNYTmc5K0lxRTBuOFlZNQpuSDlNOWx5WStoUUxjQUFPTVprOHZ5NVpYQkpyQWdNQkFBR2pXVEJYTUE0R0ExVWREd0VCL3dRRUF3SUNwREFQCkJnTlZIUk1CQWY4RUJUQURBUUgvTUIwR0ExVWREZ1FXQkJRQnJmOGtxaWtwMkdiZWxXMHhhdzNOTlB4SjBUQVYKQmdOVkhSRUVEakFNZ2dwcmRXSmxjbTVsZEdWek1BMEdDU3FHU0liM0RRRUJDd1VBQTRJQkFRQjlHeFZGeFM0SQo0bERrR2Q3L3IrSlRJZE5MRW5uNUdnMklxZW44djFaMEtTWUdSZ3RMT25UT25vOHZMTk5lNnhHRTRLdkZjTDZDCkhWWjY3SzRXSDNIV1I2VXd5VWxacE1Xck43d0VlekZEdWJKbDd0bTA5OVJad01HK2dmdkRuOExlV0Nld04vdjYKWGtTd3V5N3Vkc0p3dFREMlhnbEdJcmFLREtHWUl3NXZ1NUVqR0F6N1ZxU2ZyNzBTbHEyQzJSbmlZbkhibmt1SgprMFBEb1d6bXdDVERPbk5QcXVOZFZ4T1lCK1FycWdWY0FTSThiVThhVkszc21TM05uZ1MvdEVIdC9sR21aQlFSCitKNWlOQ0p5K2djZ2RGNFN1VEZ2TWFjU29obGFwWlRPVE95QVV6ZU42NFU0bTc3UmxtdkJYTG14WlM1VU9kVVAKeTVUbkswcHF3aEJ0Ci0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K |base64 -d|openssl x509 -noout -text
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 7010362768650409617 (0x6149cfcbac081691)
Signature Algorithm: sha256WithRSAEncryption
Issuer: CN = kubernetes
Validity
Not Before: Sep 27 07:35:28 2025 GMT
Not After : Sep 25 07:40:28 2035 GMT
Subject: CN = kubernetes
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (2048 bit)
Modulus:
00:e2:62:6d:e6:9b:a4:9a:dd:fa:c2:1e:87:ab:6c:
ad:da:2c:b2:ad:c4:ea:8b:f4:6c:0c:47:13:ce:7e:
14:a7:3c:12:d5:b6:ef:38:61:60:66:28:b2:8e:a8:
95:15:cb:77:a9:83:48:fb:cc:64:67:87:3a:41:a4:
3d:cb:3a:e2:7b:f2:98:7f:3b:f1:b8:3a:20:24:56:
3c:9f:9f:21:26:04:b5:b0:48:f2:2a:2d:2c:41:b6:
41:c9:4d:0c:90:c3:4a:8b:40:82:26:03:50:de:55:
35:fe:a2:f2:0c:27:df:e9:5e:dd:37:aa:33:1c:4c:
87:d1:89:1e:b3:86:3e:97:7c:20:de:ef:5e:fb:78:
93:79:37:80:ea:bf:c7:f6:ad:da:19:bc:c2:58:3c:
ea:44:bf:97:c1:15:85:8b:e0:2c:56:0c:55:92:f4:
40:97:67:02:04:7a:02:76:29:d0:3b:70:30:cb:68:
99:57:1b:05:d6:b1:2a:de:0a:1e:b6:51:f2:90:f1:
0a:e5:0e:f1:0d:a0:61:5c:52:7f:04:dc:4d:c4:78:
42:1e:74:7a:b1:1e:92:58:5a:80:11:2c:90:d2:61:
c5:cd:83:df:88:a8:4d:27:f1:86:39:9c:7f:4c:f6:
5c:98:fa:14:0b:70:00:0e:31:99:3c:bf:2e:59:5c:
12:6b
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Key Usage: critical
Digital Signature, Key Encipherment, Certificate Sign
X509v3 Basic Constraints: critical
CA:TRUE
X509v3 Subject Key Identifier:
01:AD:FF:24:AA:29:29:D8:66:DE:95:6D:31:6B:0D:CD:34:FC:49:D1
X509v3 Subject Alternative Name:
DNS:kubernetes
Signature Algorithm: sha256WithRSAEncryption
Signature Value:
7d:1b:15:45:c5:2e:08:e2:50:e4:19:de:ff:af:e2:53:21:d3:
4b:12:79:f9:1a:0d:88:a9:e9:fc:bf:56:74:29:26:06:46:0b:
4b:3a:74:ce:9e:8f:2f:2c:d3:5e:eb:11:84:e0:ab:c5:70:be:
82:1d:56:7a:ec:ae:16:1f:71:d6:47:a5:30:c9:49:59:a4:c5:
ab:37:bc:04:7b:31:43:b9:b2:65:ee:d9:b4:f7:d4:59:c0:c1:
be:81:fb:c3:9f:c2:de:58:27:b0:37:fb:fa:5e:44:b0:bb:2e:
ee:76:c2:70:b5:30:f6:5e:09:46:22:b6:8a:0c:a1:98:23:0e:
6f:bb:91:23:18:0c:fb:56:a4:9f:af:bd:12:96:ad:82:d9:19:
e2:62:71:db:9e:4b:89:93:43:c3:a1:6c:e6:c0:24:c3:3a:73:
4f:aa:e3:5d:57:13:98:07:e4:2b:aa:05:5c:01:22:3c:6d:4f:
1a:54:ad:ec:99:2d:cd:9e:04:bf:b4:41:ed:fe:51:a6:64:14:
11:f8:9e:62:34:22:72:fa:07:20:74:5e:12:b9:31:6f:31:a7:
12:a2:19:5a:a5:94:ce:4c:ec:80:53:37:8d:eb:85:38:9b:be:
d1:96:6b:c1:5c:b9:b1:65:2e:54:39:d5:0f:cb:94:e7:2b:4a:
6a:c2:10:6d
# 客户端证书文件及路径,此处创建了软链接
[root@k8s-master01 ~]# ll /var/lib/kubelet/pki/kubelet-client-current.pem
lrwxrwxrwx 1 root root 59 Sep 27 2025 /var/lib/kubelet/pki/kubelet-client-current.pem -> /var/lib/kubelet/pki/kubelet-client-2025-09-27-15-40-33.pem
# 查看软链接文件
[root@k8s-master01 ~]# cat /var/lib/kubelet/pki/kubelet-client-current.pem
-----BEGIN CERTIFICATE-----
MIIDMzCCAhugAwIBAgIIenB0IC4Ql88wDQYJKoZIhvcNAQELBQAwFTETMBEGA1UE
AxMKa3ViZXJuZXRlczAeFw0yNTA5MjcwNzM1MjhaFw0yNjA5MjcwNzQwMjhaMEYx
FTATBgNVBAoTDHN5c3RlbTpub2RlczEtMCsGA1UEAxMkc3lzdGVtOm5vZGU6azhz
LW1hc3RlcjAxLmRpbmdpbngub3JnMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIB
CgKCAQEAt0Xr1TV2HT2XUhD/nOlpUFVi0U+88jr/bvr8kUJ9/bOGEYyIFnjhtKq0
YcRH+FYJFUAgYR5OVOjq4jaY7LdcGYdImQQQZSIce/Ay8CA/wTjpM3LOJBG/57iD
JSg/AaTr6A1VhthNE+qnOtqEE07E0v7hakXjF41EpKHwneQEf/auKoNaFob1pTjp
inR4qOE5ocXCb8LDvmrnfJY88SKxguubQETtMii7oR2LsNyNHSC+9JUlrGtnPBnA
PBNR0B2W5BWb8B0QYFZy/fuN8ILczBs50DK3cqLIceEfQFcEipUuXzOoH+J6uFR3
S4Yz5qiMdZH/yhwJRxKZm2Xg1liiIQIDAQABo1YwVDAOBgNVHQ8BAf8EBAMCBaAw
EwYDVR0lBAwwCgYIKwYBBQUHAwIwDAYDVR0TAQH/BAIwADAfBgNVHSMEGDAWgBQB
rf8kqikp2GbelW0xaw3NNPxJ0TANBgkqhkiG9w0BAQsFAAOCAQEARjLIR1MCydEx
DidG7GjI1o+oDachcNMWeZDwDOH7ZlJ1lrB3QWBvYnunNPRndSWgkZqHg4m4+Adr
KA89FL/8xDU98VvdYQWMKsEAHbIX2oIHnS+vZldH7a2UE9rjKaPXNp1IPqJEu4b3
G2JH3RwBZOQrgtu+ntZO+V/3YoCPhYZBTmsgum0WyYz92VatwLdb3cXRZ+G/oEJv
QkredmvxUipU8H6CApo2MVHGk9GCt9wfYBixXVrODEK9FuRFzUwYBUi94Y0NGikY
44Ao+Hhf0nN9DfPyb38iJ9W/xL4XpLOFYyr5hLnrbxTckGUEOXOIHrCgqInTR4V6
LWUvG2tZEA==
-----END CERTIFICATE-----
-----BEGIN RSA PRIVATE KEY-----
MIIEogIBAAKCAQEAt0Xr1TV2HT2XUhD/nOlpUFVi0U+88jr/bvr8kUJ9/bOGEYyI
FnjhtKq0YcRH+FYJFUAgYR5OVOjq4jaY7LdcGYdImQQQZSIce/Ay8CA/wTjpM3LO
JBG/57iDJSg/AaTr6A1VhthNE+qnOtqEE07E0v7hakXjF41EpKHwneQEf/auKoNa
Fob1pTjpinR4qOE5ocXCb8LDvmrnfJY88SKxguubQETtMii7oR2LsNyNHSC+9JUl
rGtnPBnAPBNR0B2W5BWb8B0QYFZy/fuN8ILczBs50DK3cqLIceEfQFcEipUuXzOo
H+J6uFR3S4Yz5qiMdZH/yhwJRxKZm2Xg1liiIQIDAQABAoIBAAkbitJLMdXW9bbr
7IfzrkdO6iluRcl6PRXBMapWT5FUyb83G89iFA7r9lxvA9SURSdIZIa7zTcfzAX2
ojenqDmfvqMIz94p78uiiCV+tMX5YHCTrlxq6JdI7nUUpuzoZGcuInRTbQeMWOGH
2M0zOny+kp0hYMOodYmcGPgy5WmM1ybswyH9ZAP+rxmjX/KNfMBvw8crE7lNsumM
iQYMv4wruiYCaBuQq2cCxIRVfTyFKYM/pNN3RXzRxBS48SClRbWXn3GzJHsUpJE5
v5Fk93I17yIG0goOjPPZj6QF6nd0nxfb8ajJBmWknv1thjho5wLFXzAs6lxZY6OG
zzv04bECgYEA05zPmp/Z4WvkZLZvWvmLSFGQm2pE1iNF995RYPAsP/49zxvB3ocH
BfrrG2NyhFPKny88Vf38PH/WXaqrLESawZcM/6nX3/DYbtkVSj4GD4UVOUcreYxY
i8RtxoJ9YogerLDoPdoRL8CYRNvfrgW3R8BZlMzd3XCS34o1ntEyxXcCgYEA3bdW
hKO4/rwKw6/LAy9hUP88TeeWGYgq1IL1PCN47XPyKJIzV8XsBmrKNuWv1nJ+diQV
tVcUulraHBF7z0T0l/PirETPLGzDR2ihyNOl7Lib39a5kzoRV5d+xMb4wNc1KJl+
KzSw2J+2TI99/ZVMnwjjfx2+4jowfoHPQz+/GycCgYALF13+QcCewxPuf21ovEmj
mbrVmoVPH/wr2Lg1N4FqPT4qG89WhYdFtfgasGSxMN8e5s/nxe8xkJXAxRBBurrN
yMgConlRIIOHk9M81/FjYNtS7DsIHOYLNVl3nSFLR80ryf3yN/rMoPCaM1gO+/e2
SAup8+7xC1R3aPwUfeyGUwKBgBzPagqqS6uuO6fZ/ANZ8MdZozhsU3DV5NrgeYVr
Bpe0bU8gUFOjgFwFHGmtxv+SuSQY5ElAG41rqNPk4bW5PB9Sra288z7Ok0GAMyWp
evIbuwWHHW4oKYC8Sti/EivcyyePanmqyyAbANFKBBEjiWVQ/l7SOq+i6BJIQ+p1
KhwZAoGALZ3dvjtJj9g/U2swvJskBhcEfGl/LFG8oQ+9oWbbjezKPZrb0HxqVU7h
pL5ENC0l+uH04LH8d1W2Zrp4bIGTrisyU0l2XTD2fSY8duPk8k8pSRyOHHp9jX7j
CiNHS2as6PWIIis+UfuZ3L2vdT2PKM1tLbpE835cdglb7oJX1cY=
-----END RSA PRIVATE KEY-----
# 升级kubelet的客户端证书
# 修改kubelet.config文件,这里将admin.conf有效的证书信息和私钥信息直接复制使用
# 首先备份原文件
[root@k8s-master01 ~]# cp /etc/kubernetes/kubelet.conf{,.bak}
[root@k8s-master01 ~]# tail -n2 /etc/kubernetes/admin.conf >> /etc/kubernetes/kubelet.conf
## 删除其中多余的两行信息
[root@k8s-master01 ~]# vim /etc/kubernetes/kubelet.conf
#...
client-certificate: /var/lib/kubelet/pki/kubelet-client-current.pem
client-key: /var/lib/kubelet/pki/kubelet-client-current.pem
#...
# 复制文件到其他节点
[root@k8s-master01 ~]# scp /etc/kubernetes/kubelet.conf 11.0.1.1{1..3}:/etc/kubernetes/
# 更新kubeconfig文件
[root@k8s-master01 ~]# cp /etc/kubernetes/admin.conf ~/.kube/config
# 验证集群信息
[root@k8s-master01 ~]# kubectl get nodes
NAME STATUS ROLES AGE VERSION
k8s-master01.dinginx.org Ready control-plane 579d v1.35.0
k8s-node01.dinginx.org Ready <none> 579d v1.35.0
k8s-node02.dinginx.org Ready <none> 579d v1.35.0
k8s-node03.dinginx.org Ready <none> 415d v1.35.0
注意:也可选择创建新的 kubelet-client-20xx-xx-xx-xx-xx-xx.pem 文件并更新软链接。
[root@k8s-master01 ~]# ls /var/lib/kubelet/pki/ -hl
total 20K
-rw------- 1 root root 2.8K Sep 27 2025 kubelet-client-2025-09-27-15-40-33.pem
lrwxrwxrwx 1 root root 59 Sep 27 2025 kubelet-client-current.pem -> /var/lib/kubelet/pki/kubelet-client-2025-09-27-15-40-33.pem
Kubernetes证书实现“长期有效”
虽然定期续期是标准的运维流程,但对于某些测试环境或希望极大减少维护频率的场景,我们可以在集群初始化时,通过修改kubeadm源码来生成有效期极长的证书,实现所谓的“永久生效”。注意:此操作建议仅在创建新集群时执行,生产环境请谨慎评估安全风险。
安装必要的工具
首先需要在编译机器上安装编译所需的工具。
# 安装工具包
[root@k8s-node03 ~]# apt install -y make git
# 查看kubeadm版本,这里是v1.35.0
[root@k8s-node03 ~]# kubeadm version
kubeadm version: &version.Info{Major:"1", Minor:"35", EmulationMajor:"", EmulationMinor:"", MinCompatibilityMajor:"", MinCompatibilityMinor:"", GitVersion:"v1.35.0", GitCommit:"66452049f3d692768c39c797b21b793dce80314e", GitTreeState:"clean", BuildDate:"2025-12-17T12:39:26Z", GoVersion:"go1.25.5", Compiler:"gc", Platform:"linux/amd64"}
下载源码
下载与集群版本一致的Kubernetes源码。
[root@k8s-node03 /data]# git clone --depth 1 --branch v1.35.0 https://github.com/kubernetes/kubernetes.git
[root@k8s-node03 /data]# cd kubernetes/
[root@k8s-node03 /data/kubernetes]# du -sh ../kubernetes/
380M ../kubernetes/
# 验证信息
[root@k8s-node03 /data/kubernetes]# git log
commit 66452049f3d692768c39c797b21b793dce80314e (grafted, HEAD, tag: v1.35.0)
Author: Kubernetes Release Robot <k8s-release-robot@users.noreply.github.com>
Date: Wed Dec 17 12:32:06 2025 +0000
Release commit for Kubernetes v1.35.0
修改源码证书有效期
找到并修改控制证书有效期的常量。
# 修改源码信息
[root@k8s-node03 /data/kubernetes]# vim cmd/kubeadm/app/constants/constants.go
#...
// CertificateValidityPeriod defines the validity period for all the signed certificates generated by kubeadm
//CertificateValidityPeriod = time.Hour * 24 * 365
CertificateValidityPeriod = time.Hour * 24 * 365 * 100 # 组件证书设置100年
// CACertificateValidityPeriod defines the validity period for all the signed CA certificates generated by kubeadm
//CACertificateValidityPeriod = time.Hour * 24 * 365 * 10
CACertificateValidityPeriod = time.Hour * 24 * 365 * 1000 # CA根证书设置1000年
#...
# 编译
make all WHAT=cmd/kubeadm GOFLAGS=-v
# 等待编译完成,复制二进制包
[root@ubuntu1804 /usr/local/kubernetes]# ls _output/bin/kubeadm -hl
-rwxr-xr-x 1 root root 70M Mar 22 09:53 _output/bin/kubeadm
# 复制到集群节点
[root@ubuntu1804 /usr/local/kubernetes]# scp _output/bin/kubeadm 11.0.1.10:/usr/bin/kubeadm
拆除集群并重新创建
使用修改后的kubeadm二进制文件,重新初始化集群以生成长期有效的证书。
## 拆除整个集群,生产慎用!!!每个节点都需执行
kubeadm reset --cri-socket unix:///var/run/cri-dockerd.sock && rm -rf /etc/kubernetes/ /var/lib/kubelet /var/lib/dockershim /var/run/kubernetes /var/lib/cni /etc/cni/net.d /var/lib/etcd /run/flannel/
## 初始化master节点
kubeadm init --control-plane-endpoint="kubeapi.dinginx.org" --kubernetes-version=v1.35.0 --pod-network-cidr=10.244.0.0/16 --service-cidr=10.96.0.0/12 --token-ttl=0 --cri-socket unix:///var/run/cri-dockerd.sock --image-repository=registry.aliyuncs.com/google_containers
# worker节点加入集群
kubeadm join kubeapi.dinginx.org:6443 --token 3s16nk.tjm7fzie4glhrzxs \
--discovery-token-ca-cert-hash sha256:2be22e9b136994e593f4a8b33b1f426f568410fbf3d1e4c2814981d3e91412c2 \
--cri-socket unix:///var/run/cri-dockerd.sock
检查集群证书信息
集群创建完成后,验证证书的有效期已被极大地延长。
[root@k8s-master01 ~]# kubeadm certs check-expiration
[check-expiration] Reading configuration from the “kubeadm-config” ConfigMap in namespace “kube-system”...
[check-expiration] Use 'kubeadm init phase upload-config kubeadm --config your-config-file’ to re-upload it.
CERTIFICATE EXPIRES RESIDUAL TIME CERTIFICATE AUTHORITY EXTERNALLY MANAGED
admin.conf Mar 19, 2036 10:03 UTC 9y ca no
apiserver Mar 19, 2036 10:03 UTC 9y ca no
apiserver-etcd-client Mar 19, 2036 10:03 UTC 9y etcd-ca no
apiserver-kubelet-client Mar 19, 2036 10:03 UTC 9y ca no
controller-manager.conf Mar 19, 2036 10:03 UTC 9y ca no
etcd-healthcheck-client Mar 19, 2036 10:03 UTC 9y etcd-ca no
etcd-peer Mar 19, 2036 10:03 UTC 9y etcd-ca no
etcd-server Mar 19, 2036 10:03 UTC 9y etcd-ca no
front-proxy-client Mar 19, 2036 10:03 UTC 9y front-proxy-ca no
scheduler.conf Mar 19, 2036 10:03 UTC 9y ca no
super-admin.conf Mar 19, 2036 10:03 UTC 9y ca no
CERTIFICATE AUTHORITY EXPIRES RESIDUAL TIME EXTERNALLY MANAGED
ca Feb 26, 2126 10:03 UTC 99y no
etcd-ca Feb 26, 2126 10:03 UTC 99y no
front-proxy-ca Feb 26, 2126 10:03 UTC 99y no
从输出可以看到,组件证书有效期延长至约9年,而根CA证书的有效期更是达到了99年,这极大减少了未来证书管理的负担。希望这篇关于Kubernetes证书管理、续签与长期有效设置的详细指南,能帮助你更好地维护集群的安全与稳定。